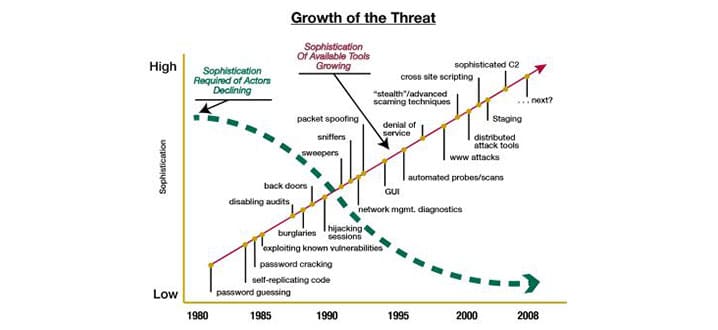
Today’s cyber threat landscape is markedly different from that of a few years ago. Experts and officials agree that the speed of attacks and their sophistication has changed dramatically. Another vital difference lies in their diversity. Cyber risks threaten the benefits, whether economic, political or social that the human invention of cyberspace can offer.
The increasing importance of cyber as a new “Great Game” merits the question as to whether NATO’s current role and activities are enough. With its extensive experience and unique status as an important player in global security, should NATO play a different, more pro-active role in contributing to cyber-security globally?
Cyber attacks on the world stage
Many more states now consider cyber capabilities as a legitimate and necessary part of their strategic toolbox alongside diplomacy, economic prowess and military might. This raises concerns about whether in the near future we might witness a full-on war in cyberspace between states. Additionally, we see occasional interest in the employment of cyber capabilities by non-state actors – at present with scant evidence as to their actual use.
Nonetheless, academics such as Thomas Rid are of the view that cyber war will not take place. Experience to date on the actual uses of cyber capabilities by states suggests such capabilities are better characterised as either espionage or sabotage, making their employment most likely below the threshold of armed attack. While there is a certain logic to this argument, it is increasingly clear that some states consider cyber capabilities as an integral part of operational military capability and are not afraid to employ them as such, even if they are reluctant to acknowledge such use publicly.
Diverse cyber threats
The diversity in the ways in which cyber capabilities can be used poses one of the greatest challenges to NATO in understanding its own role when it comes to cyber defence. Two main types of cyberattack are particularly relevant in considering NATO’s role on the cyber stage. First, cyber-enabled espionage – whether at the strategic or operational level – can compromise the confidentiality of information and information systems, potentially giving away secrets and sensitive information to adversaries. Second, cyber-enabled sabotage can have important physical ramifications, especially when infrastructures such as energy or transportation networks are targeted or where data is manipulated to confuse the target and undermine command and control decision making.

The targeting of energy networks is one of many diverse cyber threats, where data is manipulated to confuse the target and undermine command and control decision-making.
In addition, NATO’s staff at all levels and in all areas can also be targeted by extortion or fraud for financial gain, or as a preliminary stage in the forms of attack identified above. The ubiquity of the Internet on mobile devices coupled with the proliferation of social media further compounds the challenge of operational security in cyberspace.
In managing these challenges, a comprehensive approach for all things cyber is required of NATO, which can accommodate these diverse and evolving threats in a single robust and agile framework.
NATO’s current offer
Viewed very simply, NATO’s cyber defence role may be split into two broad themes. The first priority is the protection of its own networks, as agreed by Allies at the NATO Summit in Wales in 2014. This is a challenging task given the expansive footprint of the Alliance at a variety of sites and operational facilities in conditions ranging from the urban metropolis of Brussels to the austere, harsh environments of deserts. In discharging this part of its cyber defence role, NATO has to ensure that the communication and information systems that the Alliance relies upon for its operations and missions are protected against threats emanating from cyberspace.

NATO offers a wide range of education, training and exercise opportunities through, for example, the NATO School in Oberammergau.
NATO’s second priority is to assist its members in developing their own cyber defence capabilities and capacity. This is done through a variety of means, including a two-year process of setting collective cyber defence targets which each Ally must sign up to, for example, the creation of a cyber defence strategy. Progress against the achievement of these jointly agreed goals is regularly reviewed. In addition, NATO offers a wide range of education, training and exercise opportunities through diverse educational institutions including the NATO School in Oberammergau and the planned Cyber Academy in Portugal. The NATO-accredited Cooperative Cyber Defence Centre of Excellence in Tallinn also plays an important role in this regard.
Combined, these activities are intended to be self-reinforcing since any network is only as strong as its weakest point. The security of the Alliance and its ability to conduct agreed tasks of collective defence, crisis management and cooperative security is, to a large extent, dependent upon the cyber-defence capability and capacity of its individual Allies.
Other international actors
Externally too, as NATO sets out its cyber case more publicly, it sits in an increasingly complex constellation of international actors. The United Nations has been deliberating the principles of norms of state behaviour in cyberspace through a special Group of Governmental Experts. This has been galvanised in part by a longstanding initiative, backed by Russia and China, to agree an international treaty regulating the use of cyberspace that may give authoritarian governments greater scope to interfere with and censor Internet content critical of their regimes.
The Organization for Security and Co-operation in Europe has adopted its second set of cyber confidence-building measures. These aim to increase transparency in relations between states by encouraging those who sign up to follow a common series of steps, such as cooperation between incident-response communities in each country.

A Technical Arrangement on Cyber Defence is signed on 10 February 2016 by the Head of the European Union’s Computer Emergency Response Team (CERT-EU), Freddy Dezeure, and the Chief of Cyber Security at the NATO Computer Incident Response Capability (NCIRC), Ian West. © NATO
Finally, the European Union (EU) is another pre-eminent actor which engages in a broad range of efforts to help raise cyber security standards among its 28 member states and the private sector. These include capacity building for civilian cyber security, support for training, increased cooperation between law enforcement to tackle cybercrime and policy making (including through binding legal tools).
NATO as a cyber enabler
The public-private character of how the Internet is governed highlights the need to work together – a key issue when reviewing NATOs role. Looking to the East, the Alliance has been recently reminded of the realities of international relations through the unilateral application of state power by Russia in the Crimea. However, cooperation between like-minded states and international organisations remains the best way to address many cyber risks.
Here are five areas where NATO could strengthen its role as a cyber enabler over the medium term:
Mainstreaming cyber defence: mainstreaming cyber defence into Alliance operations and missions by providing a clear doctrinal framework for Allies to elevate the contribution of cyber defence to operations led by NATO from a supporting to a more standalone role.
Capability development among Allies: NATO could offer a clear platform for advice and exchange of detailed good practice between Allies through a more extensive variety of formal and informal channels, including NATO’s Defence Planning Process. Such mechanisms might include an organic capability to offer on-the-ground policy, operational and technical support and advice to Allies regarding cyber-defence capability development and implementation. This might include advice on the establishment of a military cyber-security programme or brokering the exchange of good practice on resourcing for cyber defence.
Support for international norms: The Alliance might also define its international role more explicitly through advocating support, via its international engagements, for the norms of responsible state behaviour in cyberspace and cyber confidence-building measures. It should also encourage Allies to do so.
Law enforcement intelligence exchange: More could also be done through facilitating the exchange of cyber situational awareness both between Allies and other relevant international organisations, especially those that have an operational insight into how cyberspace can be misused. States can buy cheaply on the black market sophisticated cyber-attack capability that would otherwise take time and resources to develop. So interaction with law enforcement is key and practical cooperation with Interpol and Europol would represent a useful first step.
Engaging with the EU: NATO needs to cultivate its complementary role to the EU on cyber issues. It has become clichéd to talk about NATO-EU co-operation on the basis of mutual complementarity, especially given the current debate regarding hybrid warfare or grey-zone conflicts. Nonetheless, both organisations have yet to fully come to terms with how cyber issues that confront one affect the other. On the one hand, militaries rely upon critical infrastructure protection which is the provenance of EU policy-making including via legislation and industry standards. They can also benefit from the insights into criminal cyber activity that can be offered by the EU’s Cyber Crime Centre in The Hague. On the other hand, the economic prosperity of the EU member states and by extension the region as a whole can be (and is being) threatened by state-level actors whose motives may be better understood by NATO.

Interaction with law enforcement is key and practical cooperation with Interpol and Europol through intelligence exchange would represent a useful first step.
Of course, such mechanisms would require agreement by Allies on crucial aspects, such as NATO’s remit when it comes to civilian infrastructure, which would take time to mature. Similarly, establishing co-operation with law enforcement would require a great deal of effort due to the legitimate and longstanding legal and cultural concerns about cooperation between defence and law enforcement. There are glimmers of progress however. One such example is the recently signed technical arrangement on the exchange of information between the respective NATO and EU incident-response teams.
Such suggestions, represent realistic and practical opportunities for NATO to bring its global brand as the security provider par-excellence into the evolving “Cyber Great Game”.
The opinions expressed in this article represent those of the author and do not represent official opinion or policy of NATO.